Free Hash Generator
Type or paste text and instantly see cryptographic hashes computed using the Web Crypto API (crypto.subtle.digest), the same cryptographic engine that powers HTTPS and TLS in every modern browser. All four SHA-2 family algorithms run simultaneously as you type — SHA-256 (256-bit, the industry standard used in blockchain, digital signatures, and file integrity), SHA-384 (384-bit, common in government and financial systems), SHA-512 (512-bit, the strongest variant with superior performance on 64-bit processors), and SHA-1 (160-bit, included for legacy compatibility but deprecated by NIST since 2011 after the Google/CWI SHAttered collision attack proved it insecure). Color-coded output with bit-length display, one-click copy, and real-time avalanche-effect demonstration — change a single character and watch every hash change completely. All computation is local; your text never leaves your device.
What Is a Cryptographic Hash and Why Does It Matter?
A cryptographic hash function takes any input — a single character, a full document, an entire hard drive — and produces a fixed-size output called a hash or digest. The output is deterministic (the same input always yields the same hash), one-way (you cannot reconstruct the input from the hash), and collision resistant (it is computationally infeasible to find two different inputs with the same hash). Even a single-character change in the input triggers the avalanche effect, flipping roughly half the bits in the output and producing a completely different hash. These properties make cryptographic hashes fundamental to modern computing: they underpin file integrity verification (comparing SHA-256 checksums), Git version control (every commit is identified by its hash), blockchain systems (Bitcoin double-hashes each block header with SHA-256), digital signatures (the document hash is what gets signed, not the full document), TLS certificate fingerprints, content-addressable storage systems, and secure password verification.
This tool uses the Web Crypto API (crypto.subtle.digest), a W3C standard built into every modern browser that provides native, hardware-accelerated cryptographic operations. It computes four hash algorithms simultaneously as you type: SHA-256 (256-bit, the most widely deployed hash in the world), SHA-384 (384-bit, used in government and financial systems), SHA-512 (512-bit, the strongest SHA-2 variant with better performance on 64-bit processors), and SHA-1 (160-bit, included for legacy compatibility but deprecated by NIST since 2011 after the Google/CWI SHAttered collision attack). All hashing runs locally in your browser — your text is never transmitted, logged, or stored.
SHA-2 Family: SHA-256, SHA-384, and SHA-512 Explained
The SHA-2 (Secure Hash Algorithm 2) family was designed by the NSA and standardized by NIST in FIPS 180-4. It includes six variants, of which SHA-256, SHA-384, and SHA-512 are the most widely used. SHA-256 operates on 32-bit words and processes input in 512-bit blocks, producing a 256-bit digest with 128 bits of collision resistance — far beyond what any computer can brute-force. SHA-512 operates on 64-bit words and processes input in 1024-bit blocks, producing a 512-bit digest. On modern 64-bit CPUs, SHA-512 is often faster than SHA-256 because it processes twice as much data per round using the processor's native word size. SHA-384 is a truncated version of SHA-512 with different initial hash values, offering a middle ground when a longer-than-256-bit digest is required without the full 512-bit length.
NIST continues to recommend SHA-2 for all standard cryptographic applications. SHA-3 (Keccak), standardized in 2015, exists as an architectural backup using a completely different sponge construction — but SHA-2 has no known practical weaknesses, and SHA-256 remains the default choice for TLS certificates, code signing, package managers (npm, pip, Docker), blockchain protocols, and developer tooling. The Web Crypto API supports SHA-256, SHA-384, and SHA-512 natively, giving this tool access to the same FIPS-validated cryptographic implementations used by your browser for HTTPS connections.
Hash Functions in Practice: From Git Commits to Blockchain
Cryptographic hashes are woven into the infrastructure developers use every day. Git identifies every object (commit, tree, blob, tag) by its SHA-1 hash, creating a Merkle tree where any change to any file ripples up to the root hash of the repository. After the 2017 SHAttered attack proved SHA-1 vulnerable, Git adopted a hardened SHA-1DC variant and began a gradual transition to SHA-256. Bitcoin uses double-SHA-256 for its proof-of-work consensus — miners race to find a block header whose hash starts with a required number of leading zeros. Package managers like npm and pip verify downloaded packages against SHA-256 checksums to ensure nothing was tampered with in transit. Docker identifies every image layer by its SHA-256 content hash, enabling deduplication across containers. Content delivery networks use hash-based cache keys so that any content change automatically invalidates the old cached version.
For password storage, however, general-purpose hash functions like SHA-256 are the wrong tool. SHA-256 is designed to be fast, and a modern GPU can compute over 20 billion SHA-256 hashes per second — making brute-force attacks trivially effective against hashed passwords. Dedicated password hashing algorithms like Argon2id (the current OWASP recommendation), bcrypt, and scrypt are intentionally slow and memory-hard, reducing GPU throughput by a factor of millions. They also incorporate built-in salting to defeat rainbow table attacks. This tool is designed for data integrity hashing and developer workflows — for password storage, always use a purpose-built password hashing library.
Get a Personal AI Assistant
Hire an AI assistant for scheduling, reminders, inbox triage, daily coordination and more. No-code setup, fully customizable, and ready to help you save time and stay organized. Works 24/7 without breaks or burnout.
More Free Tools
More than 20 free AI tools.
How It Works
Type or paste text into the input field.
All 4 hash algorithms compute instantly as you type.
Copy any hash with one click.
Need expert help with AI?
Looking for a specialist to help integrate, optimize, or consult on AI systems? Book a one-on-one technical consultation with an experienced AI consultant to get tailored advice.
Key Features
Privacy & Trust
Use Cases
Limitations
- Does not support MD5 (not available in Web Crypto API)
- Does not support file hashing (text input only)
- SHA-1 is shown for compatibility but is not recommended for security
- Does not support HMAC or keyed hashing
Q&A SESSION
Got a quick technical question?
Skip the back-and-forth. Get a direct answer from an experienced engineer.
Frequently Asked Questions
Is this Hash Generator free?
Yes. It runs locally using the Web Crypto API and is completely free with no usage limits, no signup, and no per-hash charges. Cloud hashing APIs and developer tool subscriptions typically charge per request or per month. Because this tool executes crypto.subtle.digest() entirely in your browser, there are no server costs, so you can generate unlimited hashes for as long as you need.
Is my text sent to a server?
No. All hashing happens entirely inside your browser using the Web Crypto API (crypto.subtle.digest). Your text is never transmitted over the network, never logged, and never stored — not even temporarily. This makes it safe for hashing confidential data, internal configuration values, API keys you want to compare, or any text you would not want a third party to see. You can verify this by opening the Network tab in DevTools while typing.
What is SHA-256 and why is it the industry standard?
SHA-256 (Secure Hash Algorithm 256-bit) is a cryptographic hash function from the SHA-2 family, standardized by NIST in FIPS 180-4. It takes any input and produces a fixed 256-bit (64 hex character) digest. SHA-256 offers 128 bits of collision resistance, meaning an attacker would need roughly 2^128 operations to find two inputs with the same hash — far beyond what any computer can achieve. It is the backbone of Bitcoin and most blockchain systems, the default for Git commit signing (replacing SHA-1), the standard for TLS certificate fingerprints, and the algorithm behind most software checksum verification. It strikes the best balance between security strength and computational speed, which is why it remains the most widely deployed hash algorithm in the world.
What is the difference between SHA-256, SHA-384, and SHA-512?
All three belong to the SHA-2 family defined in NIST FIPS 180-4, but they differ in digest size and internal architecture. SHA-256 uses 32-bit words and produces a 256-bit (64 hex character) output. SHA-512 uses 64-bit words and produces a 512-bit (128 hex character) output — it is actually faster than SHA-256 on 64-bit processors because it processes data in larger chunks. SHA-384 is a truncated version of SHA-512 computed with different initial values, producing a 384-bit (96 hex character) output. For most applications, SHA-256 provides more than sufficient security. SHA-512 is preferred when you need a longer digest or are running on 64-bit hardware and want maximum throughput. SHA-384 is commonly used in government and financial systems that require a specific security margin.
Why is SHA-1 not recommended for security?
SHA-1 was formally deprecated by NIST in 2011, and in February 2017 researchers from Google and CWI Amsterdam demonstrated the first practical SHA-1 collision in an attack called SHAttered. They produced two different PDF files with identical SHA-1 hashes using approximately 2^63.1 computations — over 100,000 times faster than a brute-force attack. All major browser vendors stopped accepting SHA-1 SSL certificates that same year. SHA-1 is included in this tool for compatibility with legacy systems (some older APIs and protocols still reference it), but it should never be used for digital signatures, certificate verification, or any security-critical application. Use SHA-256 or SHA-512 instead.
Why is MD5 not included in this tool?
The Web Crypto API deliberately excludes MD5 because it is cryptographically broken beyond repair. MD5 produces a 128-bit hash, and practical collision attacks have existed since 2004 — today, collisions can be generated in seconds on consumer hardware. MD5 was infamously exploited in the Flame malware attack, which used an MD5 collision to forge a Microsoft code-signing certificate. If you need MD5 for legacy compatibility (some older systems still use it as a non-security checksum), use a dedicated JavaScript library, but never rely on it for integrity verification or security.
What are the key properties of a cryptographic hash function?
A cryptographic hash function has four essential properties. First, it is deterministic: the same input always produces the same hash. Second, it is a one-way function (preimage resistant): given a hash, it is computationally infeasible to reconstruct the original input. Third, it is collision resistant: it is extremely difficult to find two different inputs that produce the same hash. Fourth, it exhibits the avalanche effect: changing even a single bit of the input produces a completely different hash — on average, half the output bits flip. These properties together make hashes suitable for data integrity verification, digital signatures, password storage, and content-addressable storage. You can observe the avalanche effect directly in this tool by changing one character of your input and watching all four hashes change entirely.
What is the difference between hashing, encryption, and encoding?
These are three fundamentally different operations. Hashing is a one-way function that produces a fixed-size digest from any input — you cannot reverse a hash to recover the original data. It is used for integrity checks, password storage, and fingerprinting. Encryption is a two-way function that transforms data using a key so that only someone with the correct key can decrypt it back to the original — it is used for confidentiality (protecting data in transit or at rest). Encoding is a reversible data-format transformation (like Base64 or URL encoding) with no security purpose — it simply converts data into a format suitable for a specific system. The critical distinction: hashing destroys information (irreversible), encryption preserves information (reversible with key), and encoding is a public format conversion (reversible by anyone).
Why does Git use SHA-1, and is it moving to SHA-256?
Git originally chose SHA-1 in 2005 because it was fast, widely available, and considered secure at the time. Every Git object (commit, tree, blob, tag) is identified by its SHA-1 hash. After the SHAttered collision in 2017, the Git project began transitioning to SHA-256. As of Git 2.42+, experimental SHA-256 repository support is available. The transition is gradual because the entire Git ecosystem — hosting platforms, CI systems, tooling — relies on 40-character hex identifiers. For practical purposes, Git uses a hardened SHA-1 variant (SHA-1DC) that detects and rejects SHAttered-style collision attempts, which mitigates the known attack while the SHA-256 migration completes.
Why does Bitcoin use SHA-256 and not a different hash algorithm?
Bitcoin uses double-SHA-256 (hashing the output of SHA-256 a second time) for its proof-of-work system. Each block header is hashed, and miners compete to find a nonce that produces a hash starting with a required number of leading zeros. SHA-256 was chosen because it was the strongest widely-available hash function when Bitcoin launched in 2009 — it is standardized by NIST, extensively analyzed by cryptographers, and has no known practical weaknesses. The double hashing provides defense against length-extension attacks. Ethereum, by contrast, uses Keccak-256 (the algorithm that became SHA-3), and some newer blockchains use BLAKE2 or BLAKE3 for their superior performance.
Can I use SHA-256 to hash passwords?
You should not use raw SHA-256 for password hashing. SHA-256 is designed to be fast — a modern GPU like an RTX 4090 can compute roughly 22 billion SHA-256 hashes per second, meaning an attacker could test the entire RockYou password list (14 million passwords) in under a millisecond. Instead, use a dedicated password hashing algorithm: Argon2id (winner of the 2015 Password Hashing Competition and current OWASP recommendation), bcrypt, or scrypt. These algorithms are intentionally slow and memory-hard — bcrypt at cost factor 12 takes about 250ms per hash, reducing GPU throughput to approximately 200 hashes per second. They also incorporate built-in salting to prevent rainbow table attacks. This tool is designed for data integrity hashing, not password storage.
What is HMAC and how does it differ from a regular hash?
HMAC (Hash-based Message Authentication Code) combines a cryptographic hash function with a secret key to produce an authenticated hash. A regular hash like SHA-256 can be computed by anyone who has the input — it proves integrity (the data has not been tampered with) but not authenticity (who created the hash). HMAC proves both: only someone with the secret key can produce or verify the HMAC. It is widely used in API authentication (AWS Signature V4, Stripe webhook verification), JWT token signing, and secure cookie validation. HMAC also protects against length-extension attacks that can affect raw SHA-256 hashes. This tool computes standard (non-keyed) hashes; for HMAC computation, use a dedicated HMAC tool or the Web Crypto API sign() method with an HMAC key.
What is SHA-3 and how does it compare to SHA-2?
SHA-3 (Keccak) was standardized by NIST in 2015 as FIPS 202 to serve as an independent alternative to the SHA-2 family. It uses a fundamentally different internal structure called a sponge construction, compared to the Merkle-Damgard construction used by SHA-1 and SHA-2. This architectural diversity means that a theoretical breakthrough attacking SHA-2 would not affect SHA-3, and vice versa. In practice, both SHA-2 and SHA-3 are considered equally secure today — neither has any known practical vulnerability. SHA-2 remains far more widely deployed, and the Web Crypto API currently supports SHA-2 variants but not SHA-3. For most developers, SHA-256 remains the correct default choice.
Can I hash files with this tool?
This tool hashes text input only. For file hashing, use your operating system command line: "sha256sum filename" on Linux, "shasum -a 256 filename" on macOS, or "CertUtil -hashfile filename SHA256" on Windows. These commands use the same SHA-256 algorithm and will produce identical hashes for identical content. If you paste the exact file contents as text into this tool, you will get the same SHA-256 hash as the command-line tools — the algorithm is deterministic regardless of where it runs.
What is the Web Crypto API and why does this tool use it?
The Web Crypto API (window.crypto.subtle) is a W3C standard built into every modern browser that provides native cryptographic operations including hashing, encryption, signing, and key generation. The digest() method specifically computes cryptographic hashes. This tool uses it instead of a JavaScript hash library because the Web Crypto API runs as native compiled code inside the browser engine — it is faster, more memory-efficient, and has been rigorously audited as part of every browser security review. It supports SHA-1, SHA-256, SHA-384, and SHA-512. The API is only available in secure contexts (HTTPS or localhost), which ensures the cryptographic code itself has not been tampered with during delivery.
What is the avalanche effect and can I see it in this tool?
The avalanche effect is a property of cryptographic hash functions where a tiny change to the input — even flipping a single bit — causes roughly half the output bits to change, producing a completely different hash. This is essential for security: without it, an attacker could infer information about similar inputs by comparing their hashes. You can observe the avalanche effect directly in this tool by typing a word, noting all four hashes, then changing a single character. Every hash will change completely and unpredictably — there is no visible relationship between the old and new values. This also makes hashes useful for change detection: if two files produce the same SHA-256 hash, they are identical; if the hashes differ by even one character, the files are different.
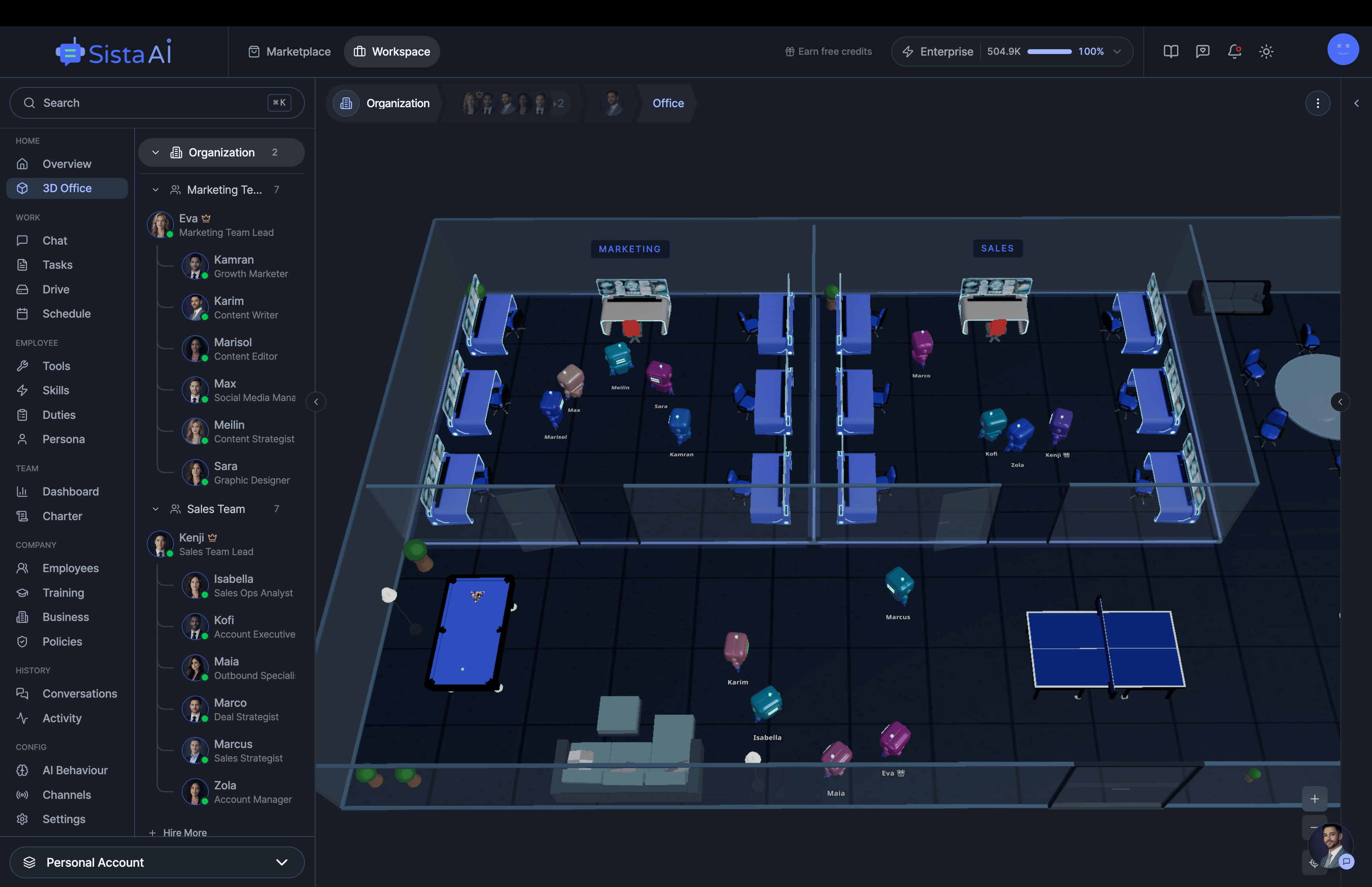
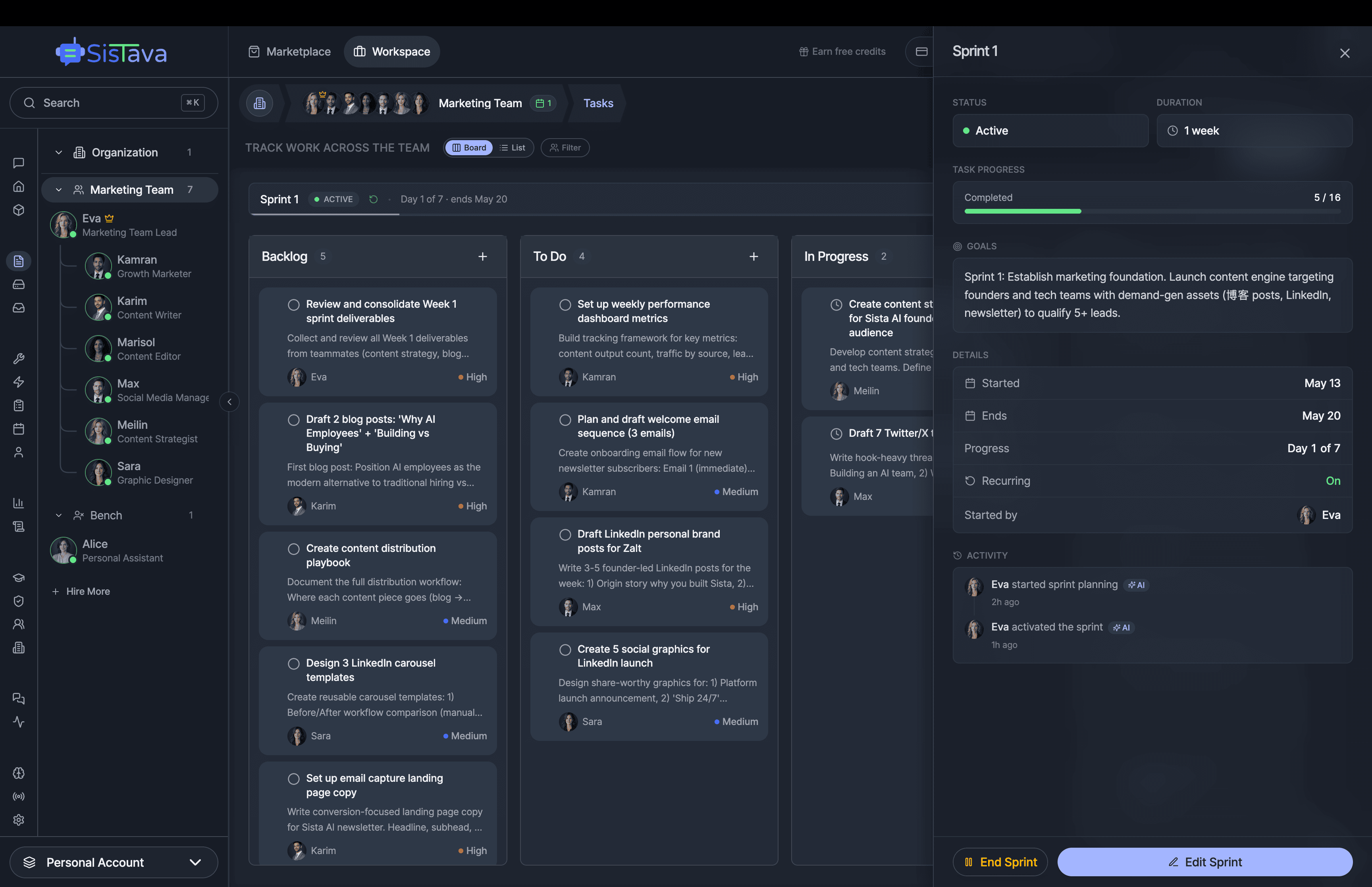
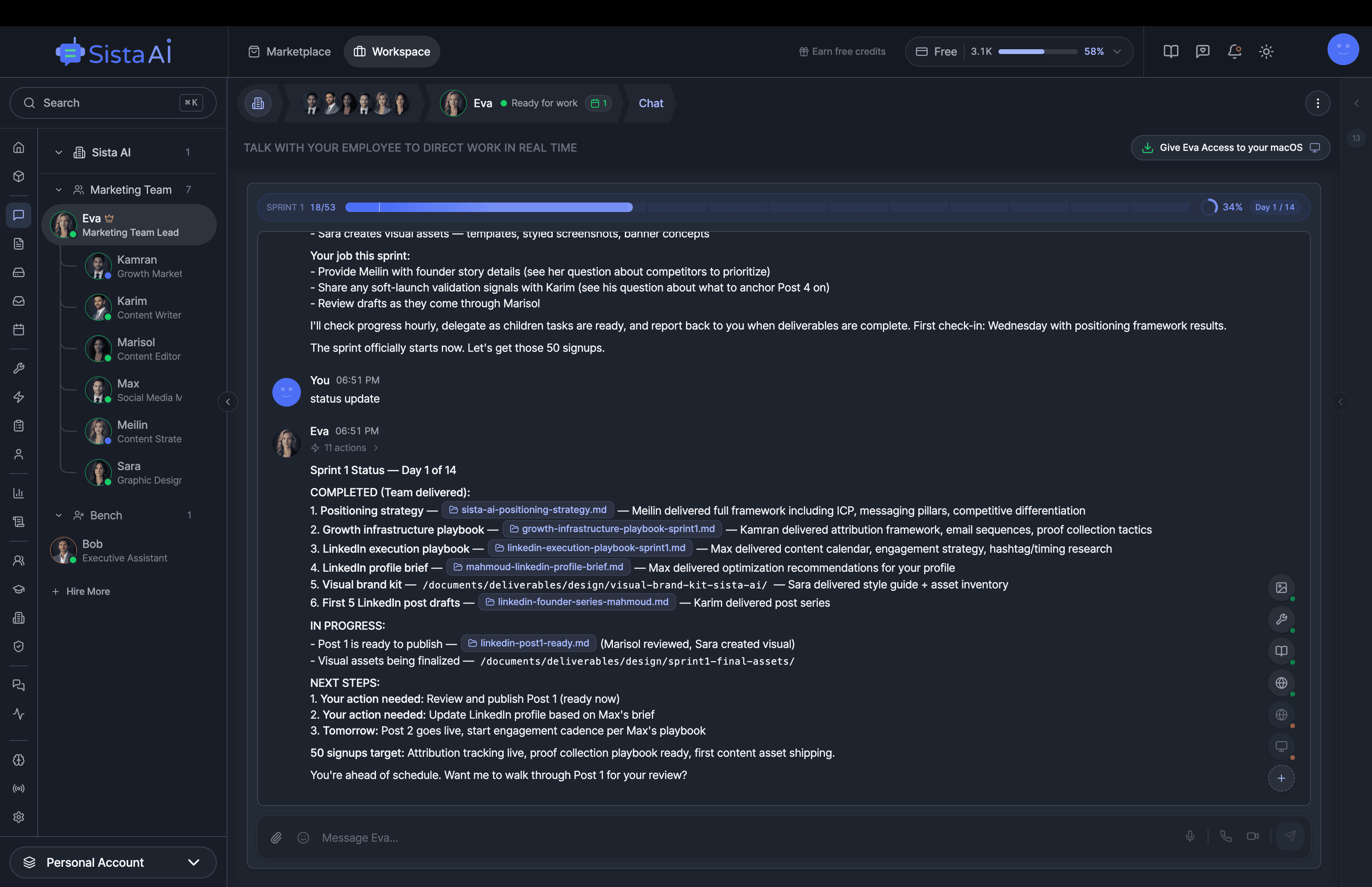
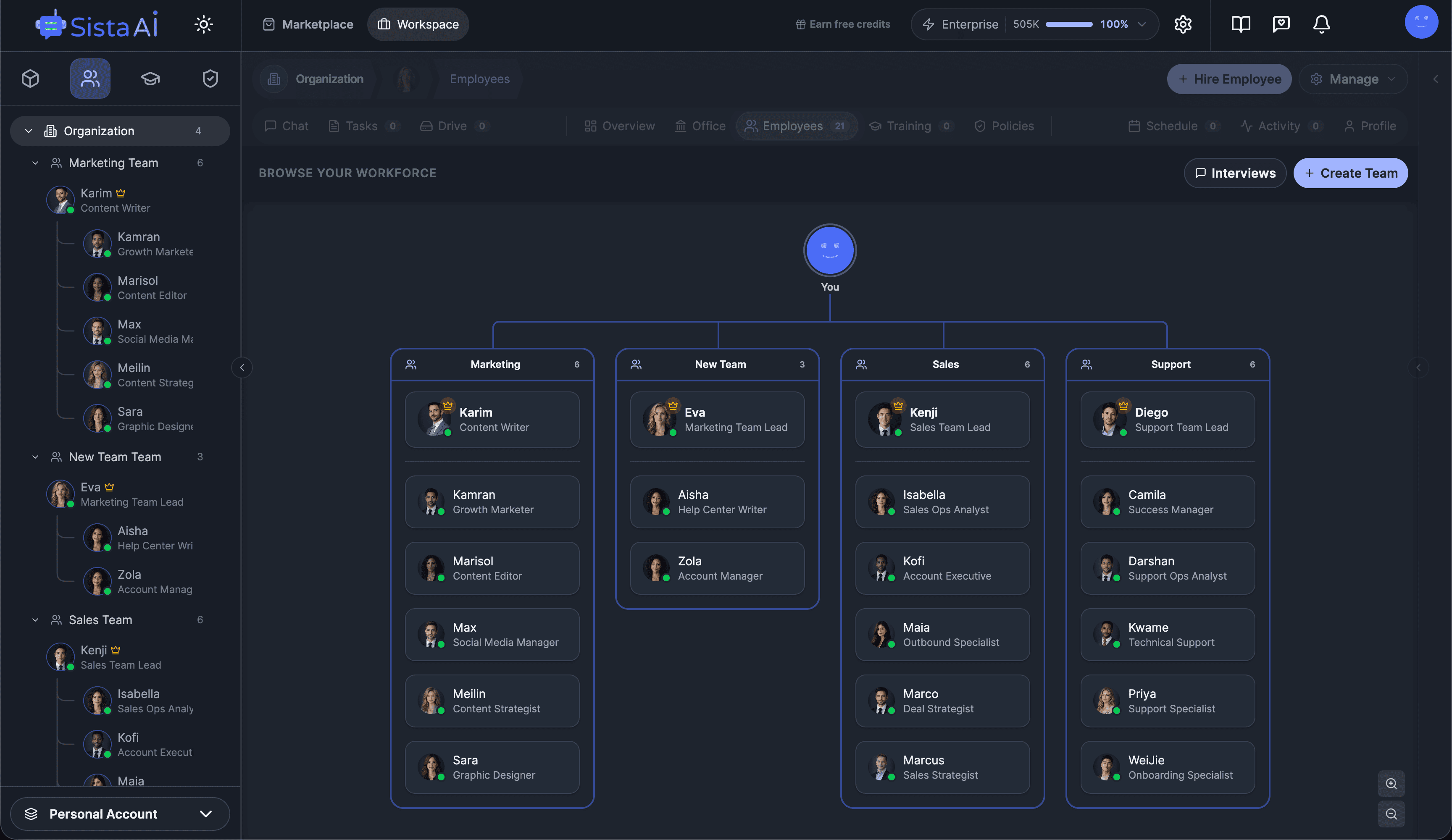
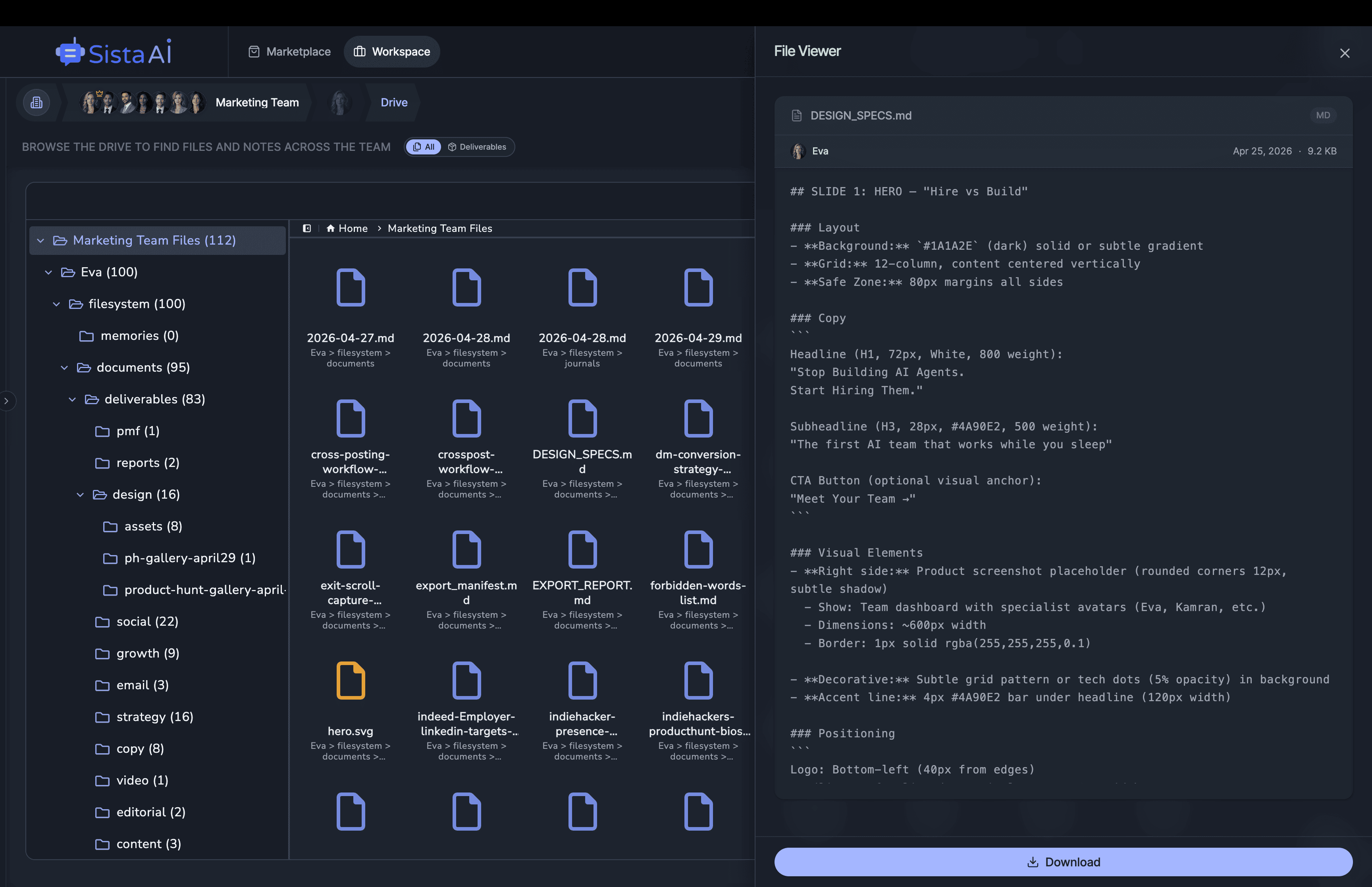
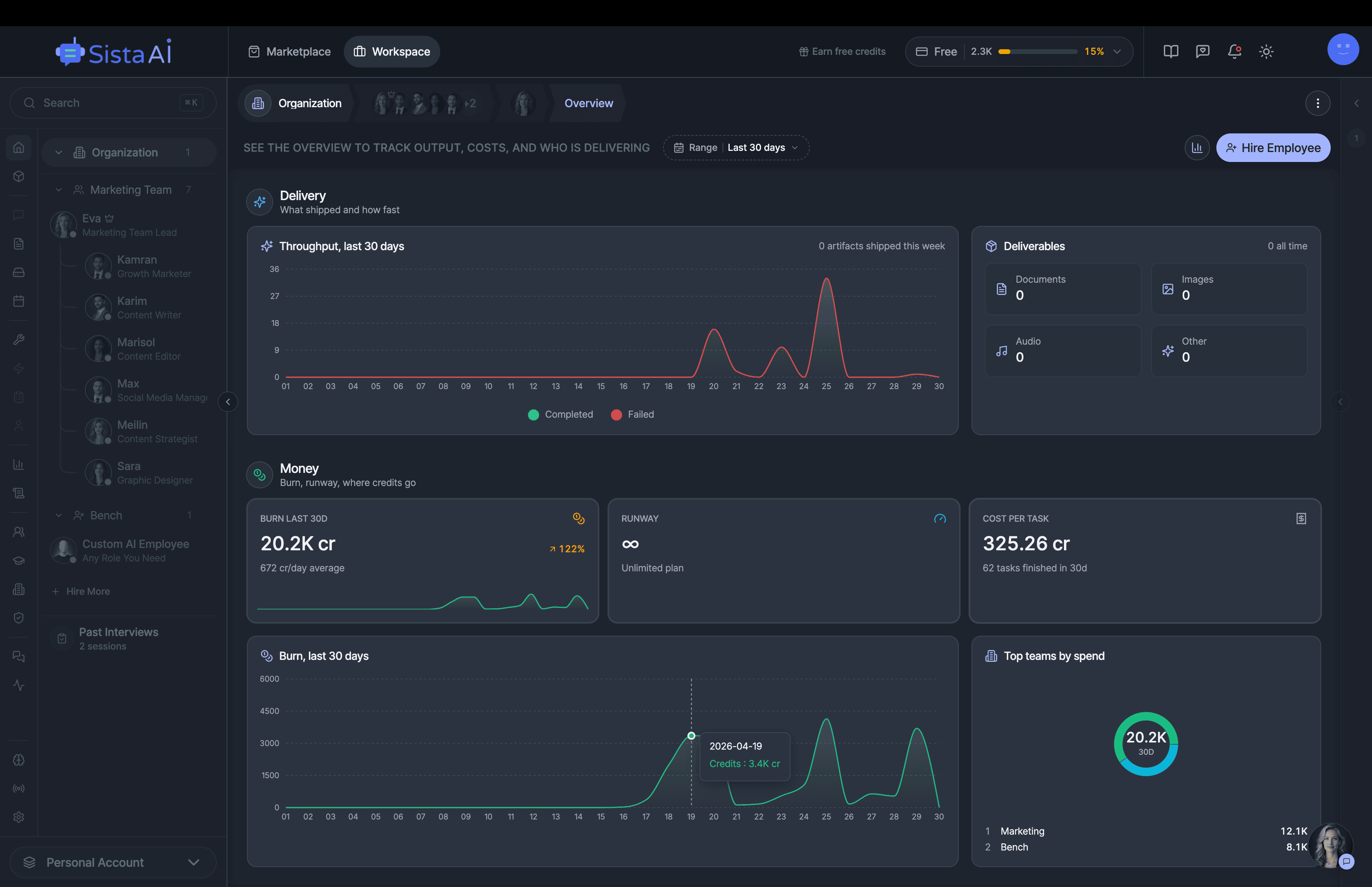
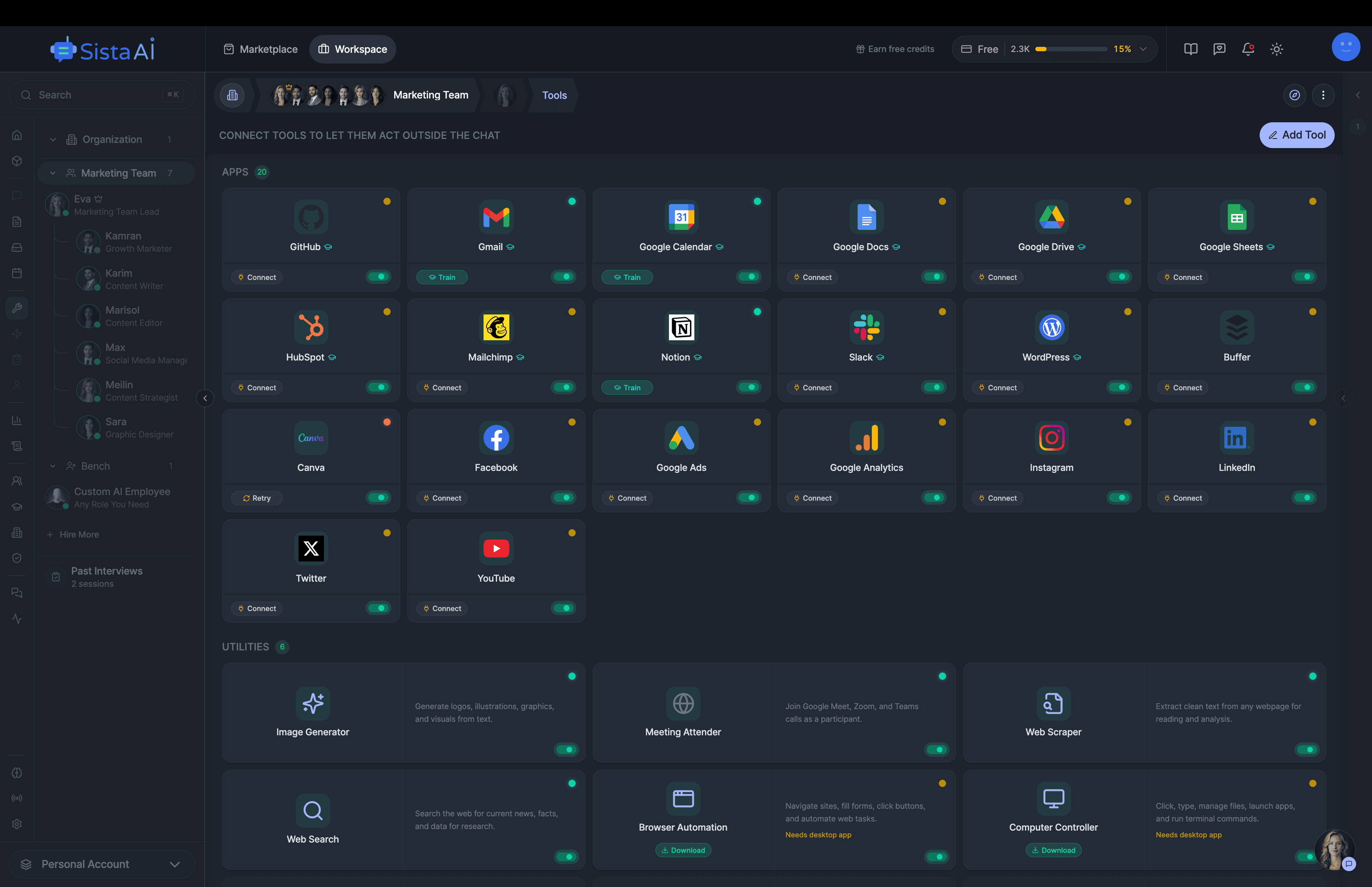
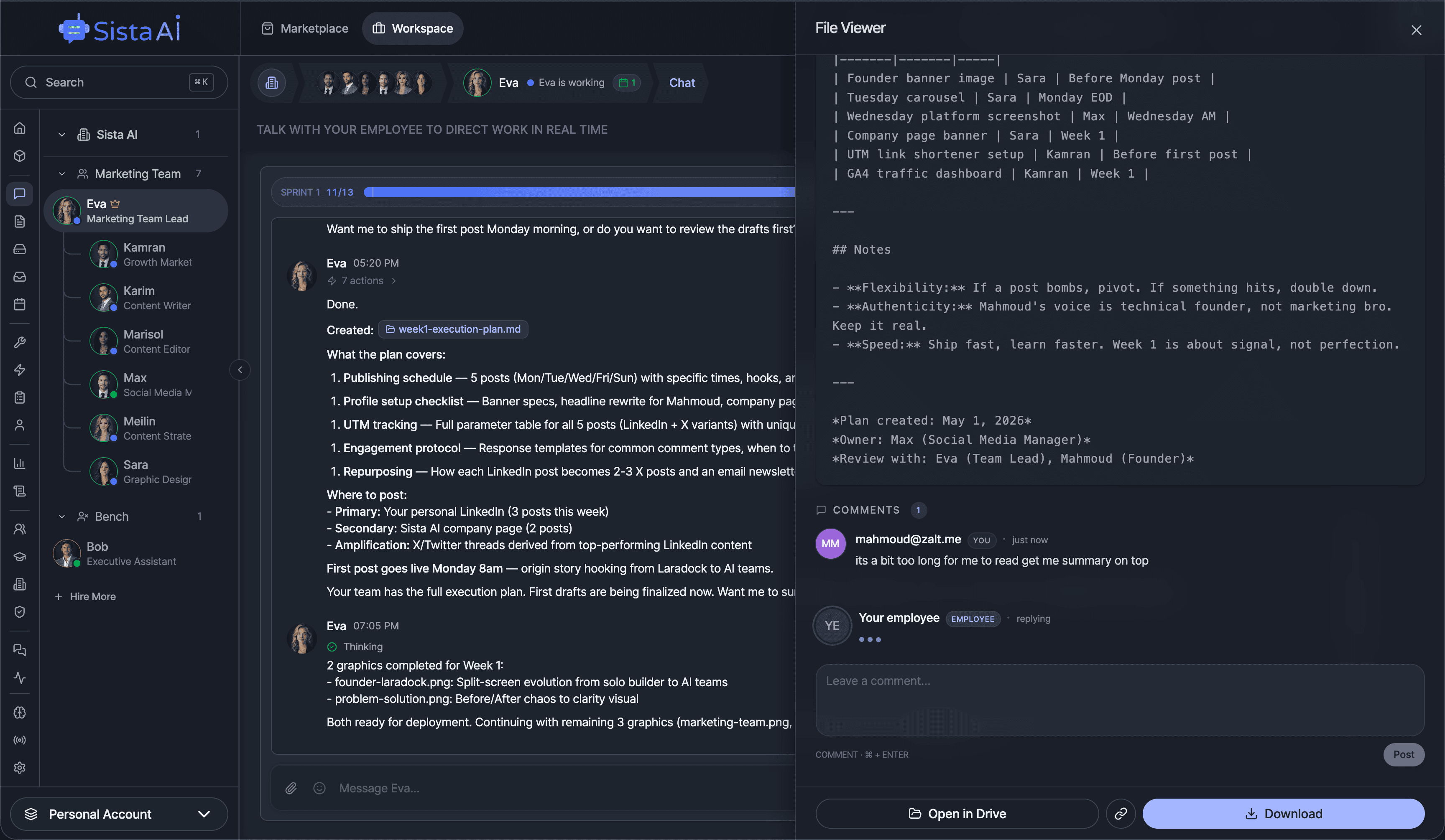
Hire Teams of AI Employees
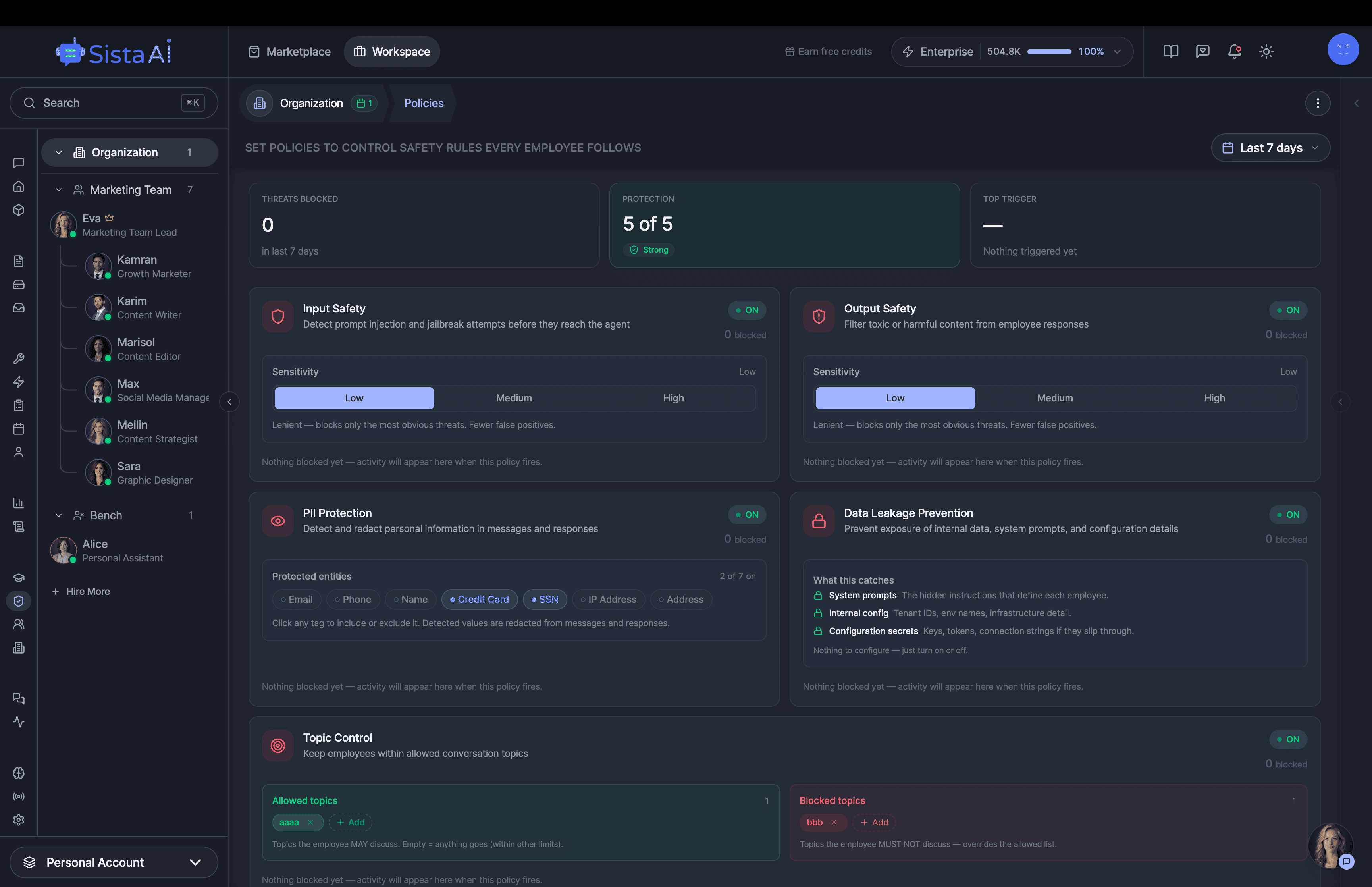
Trained teams of AI employees that work in sprints and follow OKRs to deliver real results. While you focus on strategy.
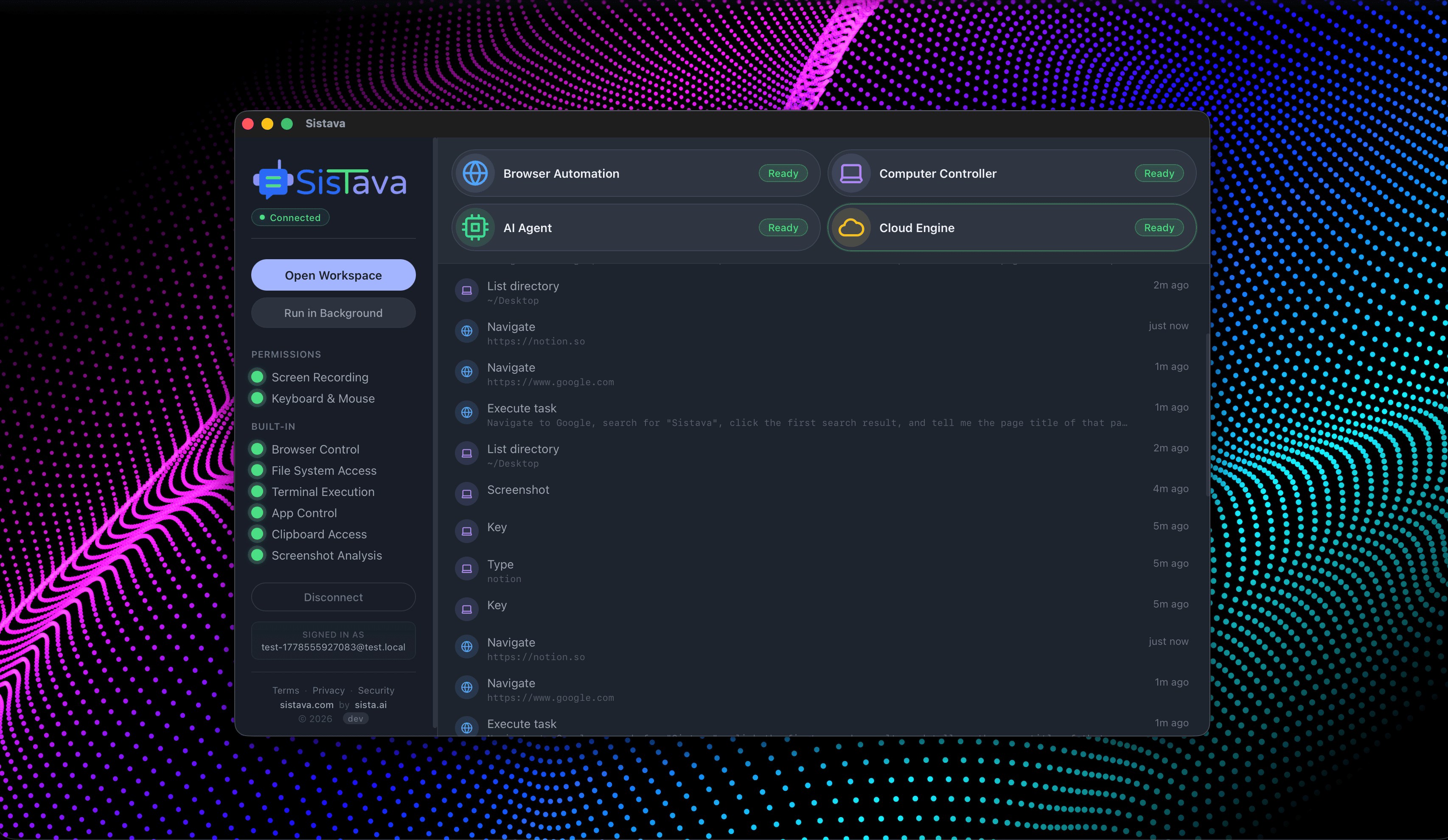
- Control your computer with natural language
- Automate any browser workflow end-to-end
- Attend and summarize your meetings
- Run teams of AI workers that collaborate in sync
- 3D office view to visualize and manage your AI workforce