Free Password Generator
Generate cryptographically secure passwords using the Web Crypto API (crypto.getRandomValues), a CSPRNG seeded by your operating system's entropy pool — the same source of randomness used by HTTPS, SSH, and TLS. NIST SP 800-63B recommends focusing on password length over complexity rules, and this tool lets you create passwords from 4 to 64 characters with full control over uppercase, lowercase, numbers, and symbols. A real-time strength indicator shows estimated entropy in bits and approximate crack time against modern GPU attacks. Keep a history of recently generated passwords and copy any of them with one click. All generation happens locally in your browser — no passwords are ever transmitted, stored, or logged on any server.
Why Random Passwords Matter and How This Generator Works
Most people create weak, predictable passwords — dictionary words, birthdays, pet names, keyboard walks like "qwerty123". These are trivially cracked by automated tools. A single NVIDIA RTX 4090 GPU can compute over 164 billion password hashes per second against NTLM, meaning an 8-character password using the full printable ASCII set falls in under 7 hours. Credential stuffing attacks use billions of breached passwords from sites like LinkedIn, Adobe, and Dropbox to break into any account that shares the same password. Have I Been Pwned now tracks over 14 billion compromised accounts. The only reliable defense is a unique, truly random password for every account.
This tool generates passwords using crypto.getRandomValues(), the Web Crypto API specified by the W3C and built into every modern browser. Unlike Math.random() — which uses a deterministic algorithm (xorshift128+ in V8) that can be reverse-engineered from observed outputs — crypto.getRandomValues() is a cryptographically secure pseudo-random number generator (CSPRNG) seeded by your operating system's entropy pool (/dev/urandom on Linux, CryptGenRandom on Windows, SecRandomCopyBytes on macOS). This is the same source of randomness that secures HTTPS connections, generates SSH keys, and creates TLS session tokens. Every password is generated entirely on your device — nothing is sent to any server, no passwords are logged, and there is zero network attack surface between generation and your clipboard.
NIST Password Guidelines: Length Over Complexity
In August 2025, NIST released Special Publication 800-63B Revision 4, overhauling its password recommendations based on years of research into how people actually create and use passwords. The most significant change: NIST dropped mandatory complexity rules. No more requiring a mix of uppercase, lowercase, numbers, and symbols. Studies found that these rules led to predictable substitution patterns — "P@ssw0rd!", "Summer2025!" — that are easily caught by dictionary attacks with common mutation rules, while frustrating users into writing passwords down or reusing them across accounts.
NIST now recommends a minimum of 15 characters for single-factor accounts (8 with MFA enabled), support for at least 64-character passwords without truncation, acceptance of all printable ASCII characters including spaces and full Unicode, screening passwords against known breached password databases, and eliminating forced periodic password rotation unless there is evidence of compromise. The math supports this shift: a 20-character lowercase-only password has 26^20 (roughly 1.9 x 10^28) possible combinations — far more than an 8-character password using all 95 printable characters (95^8 = 6.6 x 10^15). Length wins. This tool aligns with NIST guidance by supporting up to 64-character passwords and encouraging length as the primary strength factor, while still letting you add character diversity for maximum entropy at any given length.
Password Entropy, Crack Times, and Why You Need a Password Manager
Password strength is measured in bits of entropy using the formula E = L x log2(R), where L is the password length and R is the size of the character set. Lowercase only (R=26) gives about 4.7 bits per character. Adding uppercase doubles R to 52 (5.7 bits/char). Adding digits brings R to 62 (5.95 bits/char). The full printable ASCII set including symbols (R=95) gives about 6.6 bits per character. A 16-character password with all character types provides roughly 105 bits of entropy — meaning an attacker would need up to 2^105 guesses (about 4 x 10^31) to exhaust all possibilities. Even at 164 billion guesses per second on a modern GPU, that would take approximately 7.8 x 10^12 years — thousands of times longer than the age of the universe.
Of course, a strong password only protects you if it is unique to each account. Credential stuffing — where attackers replay breached username/password pairs from one site against other services — is now one of the most common attack vectors, accounting for 19% of daily authentication events at major SSO providers according to Verizon's 2025 Data Breach Investigations Report. The solution is a password manager (1Password, Bitwarden, KeePass, or similar) that stores a unique random password for every account, encrypted under a single master password. Use this tool to generate a strong master password — 20+ characters or a 6-word Diceware passphrase — then let the manager handle everything else. Pair every important account with two-factor authentication (TOTP app or FIDO2 hardware key) for defense in depth. A random password from a CSPRNG plus a password manager plus 2FA is the trifecta that NIST, OWASP, and every serious security organization recommends.
Get a Personal AI Assistant
Hire an AI assistant for scheduling, reminders, inbox triage, daily coordination and more. No-code setup, fully customizable, and ready to help you save time and stay organized. Works 24/7 without breaks or burnout.
More Free Tools
More than 20 free AI tools.
How It Works
Set your desired length and character options (uppercase, lowercase, numbers, symbols).
A strong password is generated instantly using crypto.getRandomValues — a CSPRNG built into every modern browser.
Copy the password, check its strength rating, or regenerate for a new one.
Need expert help with AI?
Looking for a specialist to help integrate, optimize, or consult on AI systems? Book a one-on-one technical consultation with an experienced AI consultant to get tailored advice.
Key Features
Privacy & Trust
Use Cases
Limitations
- Does not generate passphrases (word-based passwords like Diceware)
- Does not check passwords against breach databases like Have I Been Pwned
- Does not store or manage passwords — use a dedicated password manager for that
- Symbol set is fixed — cannot customize which specific symbols to include
- Does not support pronounceable or memorable password formats
Q&A SESSION
Got a quick technical question?
Skip the back-and-forth. Get a direct answer from an experienced engineer.
Frequently Asked Questions
Is this Password Generator completely free?
Yes. It runs locally in your browser and is 100% free with no signup, no usage limits, and no ads. Cloud-based password generators from services like LastPass, Dashlane, or NordPass require accounts or subscriptions. Because this tool generates passwords entirely on your device using the built-in Web Crypto API, there are no server costs to cover — so it will always be free.
Are the passwords truly random and secure?
Yes. This generator uses crypto.getRandomValues(), the Web Crypto API built into every modern browser. This is a cryptographically secure pseudo-random number generator (CSPRNG) seeded by your operating system's entropy pool — the same quality of randomness used by HTTPS, TLS, SSH, and other security-critical protocols. Unlike Math.random(), which uses a predictable algorithm (typically xorshift128+ in V8) and can be reverse-engineered, crypto.getRandomValues() produces output that is computationally infeasible to predict, even if an attacker knows every previous value generated.
Are my passwords sent to a server or stored anywhere?
No. All password generation happens entirely inside your browser. No passwords, settings, or usage data are transmitted to any server — not even temporarily. There are no API calls, no analytics on generated passwords, and no telemetry. This makes it safer than cloud-based generators where your password travels over the network and may be logged in server access logs. You can verify this yourself by opening the Network tab in DevTools (F12) and watching for zero requests during password generation.
How long should my password be?
NIST SP 800-63B (Revision 4, August 2025) recommends a minimum of 15 characters for single-factor accounts and at least 8 characters when multi-factor authentication (MFA) is enabled. For practical security: use at least 12 characters for everyday accounts, 16+ characters for high-value accounts (email, banking, cloud services), and 20+ characters for master passwords or encryption keys. Each additional character multiplies the number of possible combinations exponentially — a 16-character password with the full 95-character set has approximately 95^16 (about 4.4 x 10^31) possible combinations.
What makes a password strong? Is length or complexity more important?
Length is the single most important factor, and NIST now agrees. NIST SP 800-63B Revision 4 dropped mandatory complexity rules (requiring uppercase, numbers, and symbols) in favor of longer passwords that are easier to remember. The math is clear: a 20-character lowercase-only password (26^20 = 1.9 x 10^28 combinations) is stronger than an 8-character password using all 95 printable ASCII characters (95^8 = 6.6 x 10^15 combinations). That said, using the full character set at any given length maximizes entropy. The ideal approach is both long and diverse — 16+ characters with uppercase, lowercase, numbers, and symbols.
How long would it take to crack a password generated by this tool?
It depends on password length and the character set used. A single NVIDIA RTX 4090 GPU can compute approximately 164 billion NTLM hashes per second or 288 billion with overclocking. Against that speed: an 8-character password using all 95 printable characters (~52 bits of entropy) can be cracked in under 7 hours. A 12-character password (~78 bits) would take roughly 17 million years. A 16-character password (~105 bits) would take longer than the age of the universe. With bcrypt or Argon2 hashing (used by well-designed services), even an 8-character password becomes far harder to crack because these algorithms are intentionally slow — reducing attack speed to thousands of guesses per second instead of billions.
What is password entropy and why does it matter?
Entropy measures password strength in bits using the formula: E = L x log2(R), where L is the password length and R is the size of the character set. A password using lowercase letters only (R=26) gets about 4.7 bits per character, while the full printable ASCII set (R=95) gives about 6.6 bits per character. An attacker needs at most 2^E guesses to crack a password with E bits of entropy. Security researchers generally recommend 60-80 bits for standard accounts and 90-128 bits for high-security uses like master passwords or encryption keys. A 16-character password with all character types has roughly 105 bits of entropy — well into the safe zone for any current or near-future attack.
What is the difference between crypto.getRandomValues() and Math.random()?
Math.random() is a standard pseudo-random number generator (PRNG) designed for statistical simulations and games — not security. In most JavaScript engines, it uses the xorshift128+ algorithm, which is fast but deterministic: if an attacker observes a few outputs, they can predict all future values. crypto.getRandomValues() is a cryptographically secure PRNG (CSPRNG) specified by the W3C Web Crypto API standard. It draws entropy from the operating system — /dev/urandom on Linux, CryptGenRandom on Windows, SecRandomCopyBytes on macOS — making its output computationally unpredictable. Every serious security library, browser, and operating system uses CSPRNGs for key generation, token creation, and password generation. This tool exclusively uses crypto.getRandomValues().
Is this safer than online password generators that use a server?
Yes, for several reasons. Server-based generators transmit your password over the network, where it could be intercepted (even with HTTPS, the server operator sees it). The password may be logged in server access logs, application logs, or CDN edge logs. The server's random number generator may be poorly seeded or compromised. With this tool, the password exists only in your browser's memory and is never sent anywhere. The randomness comes from your own operating system's entropy pool via the Web Crypto API — not from a remote server. There is zero attack surface between generation and your clipboard.
Should I use a password manager?
Absolutely. A password generator creates strong passwords, but a password manager stores and autofills them so you never have to remember or reuse them. Reusing passwords is the single biggest risk for most people — credential stuffing attacks use billions of breached passwords (Have I Been Pwned tracks over 14 billion compromised accounts) to break into accounts that share the same password. Reputable password managers like 1Password, Bitwarden, and KeePass encrypt your vault with a master password and zero-knowledge architecture, meaning even the company cannot see your passwords. Use this tool to generate a strong master password for your manager, then let the manager generate and store unique passwords for every other account.
What is two-factor authentication and should I use it with strong passwords?
Two-factor authentication (2FA) adds a second verification step — typically a time-based one-time password (TOTP) from an authenticator app, a hardware security key (FIDO2/WebAuthn), or an SMS code — so that even if your password is compromised, an attacker cannot access your account without the second factor. NIST SP 800-63B strongly recommends MFA, especially for accounts protecting sensitive data. A strong random password plus 2FA is the gold standard for account security. Enable 2FA on every account that supports it — email, banking, cloud services, social media, and developer accounts (GitHub, AWS, etc.).
What are the most common ways passwords get compromised?
The most common attack vectors are: (1) Credential stuffing — attackers use billions of username/password pairs from previous data breaches to log into other services, exploiting password reuse. Verizon's 2025 DBIR found credential stuffing accounts for 19% of all daily authentication events at SSO providers. (2) Phishing — tricking users into entering passwords on fake login pages. (3) Brute-force and dictionary attacks — automated tools try every possible combination or common words/patterns. (4) Rainbow table attacks — precomputed hash-to-password lookup tables that can reverse unsalted password hashes in seconds. (5) Keyloggers and infostealers — malware that records keystrokes or extracts saved passwords from browsers. A randomly generated password defeats dictionary and brute-force attacks, while unique passwords for every account prevent credential stuffing from spreading.
Is a passphrase better than a random password?
It depends on the use case. A Diceware passphrase (e.g., "correct horse battery staple") is easier to memorize and type, making it ideal for master passwords or full-disk encryption passphrases where you need to type it from memory regularly. A 6-word Diceware passphrase drawn from a 7,776-word list provides about 77 bits of entropy — strong enough for most purposes. However, a random character password is more compact: a 12-character password with the full character set provides about 78 bits of entropy in 12 characters instead of 25-35. For accounts managed by a password manager (where you never type the password), random character passwords are optimal because length and memorability do not matter — only entropy does. For your master password, a long passphrase you can actually remember is often the better choice.
How many passwords have been leaked in data breaches?
The scale is staggering. Have I Been Pwned, the largest breach notification service, tracks over 14 billion compromised accounts across 1,000+ breaches. In 2025 alone, Troy Hunt indexed 2 billion newly exposed email addresses and 1.3 billion unique passwords from credential stuffing threat data — 625 million of which had never been seen before. Earlier in 2025, stealer log datasets added another 284 million unique email addresses and 244 million new passwords. The most commonly breached passwords remain predictable choices like "123456", "password", "qwerty", and "admin". A truly random password generated by a CSPRNG will never appear in these breach lists because it contains no dictionary words, patterns, or personal information.
Does NIST still recommend requiring special characters in passwords?
No. NIST SP 800-63B Revision 4 (August 2025) explicitly dropped mandatory composition rules — no more requiring uppercase, lowercase, numbers, and symbols. Research showed that these rules led to predictable patterns (P@ssw0rd!, Summer2025!) without meaningfully increasing security, while making passwords harder to remember. NIST now recommends: minimum 15 characters for single-factor accounts, support for at least 64 characters maximum length, allow all printable ASCII characters including spaces and Unicode, screen passwords against known breached password lists, and do not require periodic password changes unless there is evidence of compromise. This tool still lets you include all character types — because mixing them at a given length does increase entropy — but length alone is more important than forced complexity.
What should I do if I think my password has been compromised?
Change the password immediately on the affected account — use this tool to generate a new one. If you used the same password on other accounts (which you should never do), change those too. Enable two-factor authentication if it is not already active. Check Have I Been Pwned (haveibeenpwned.com) to see if your email appears in known breaches. Review your account for unauthorized activity — check login history, connected apps, and recovery options. If the compromised account is an email account, prioritize it because attackers can use password reset emails to compromise every other account linked to that email address.
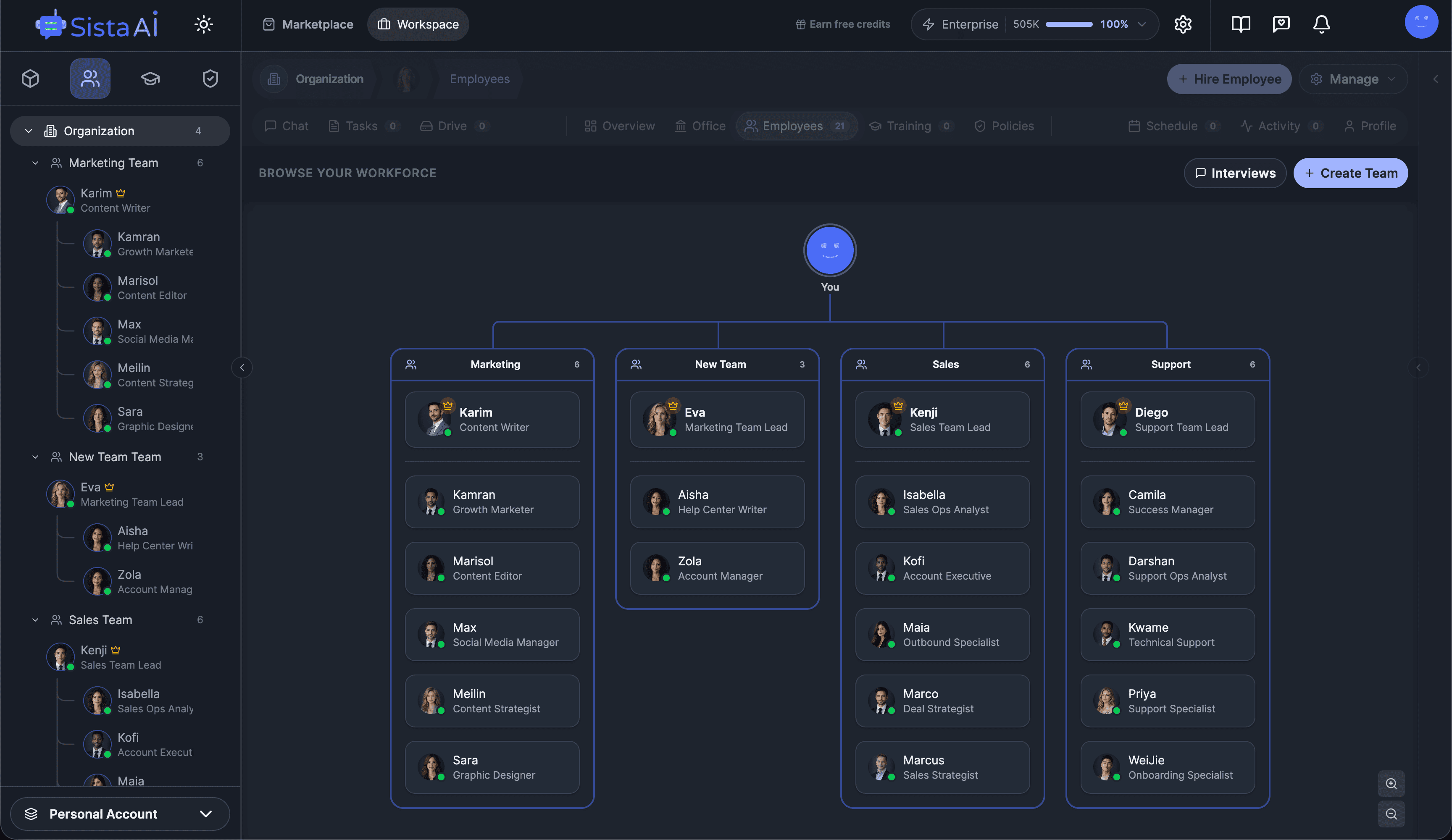
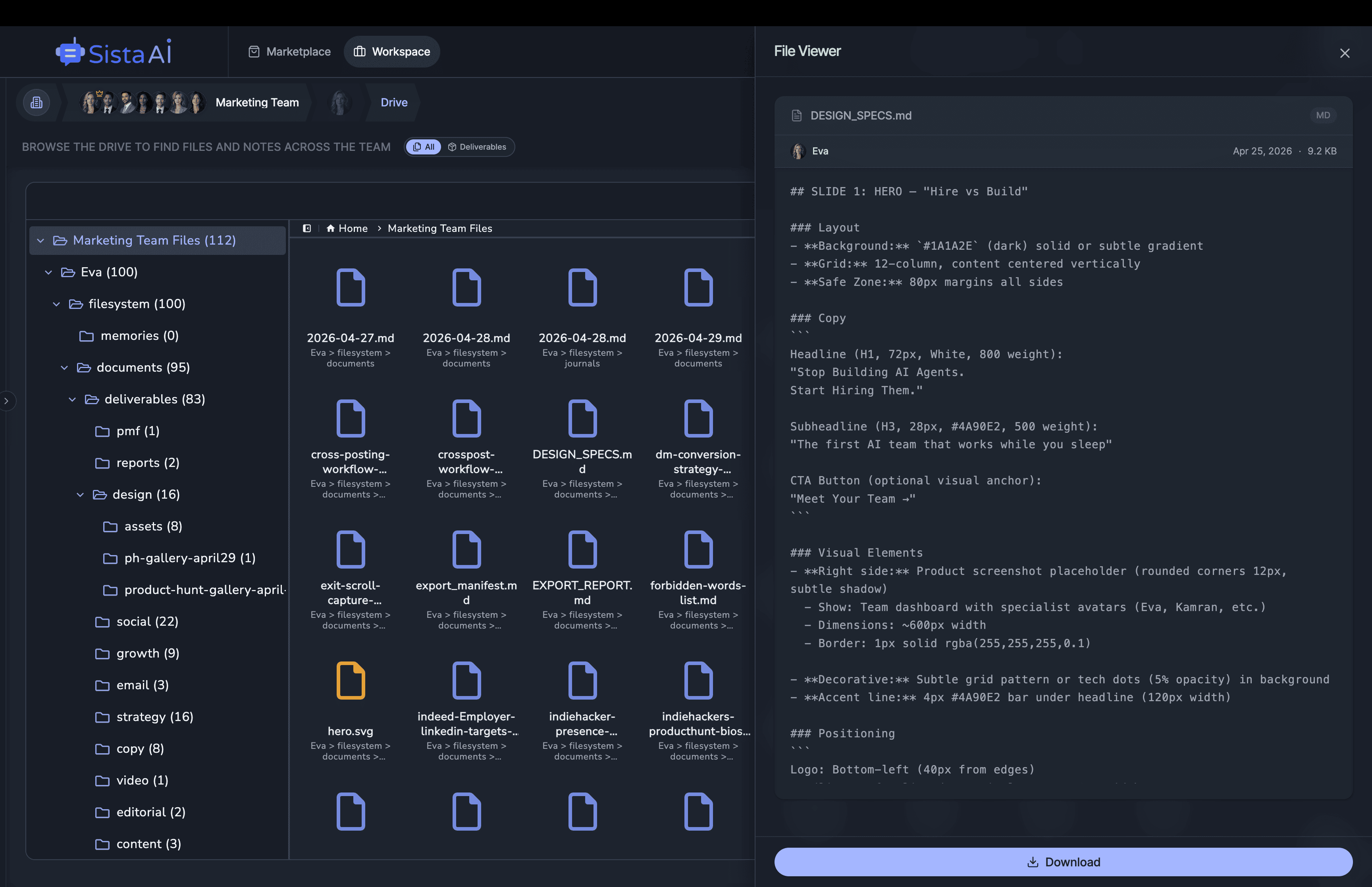
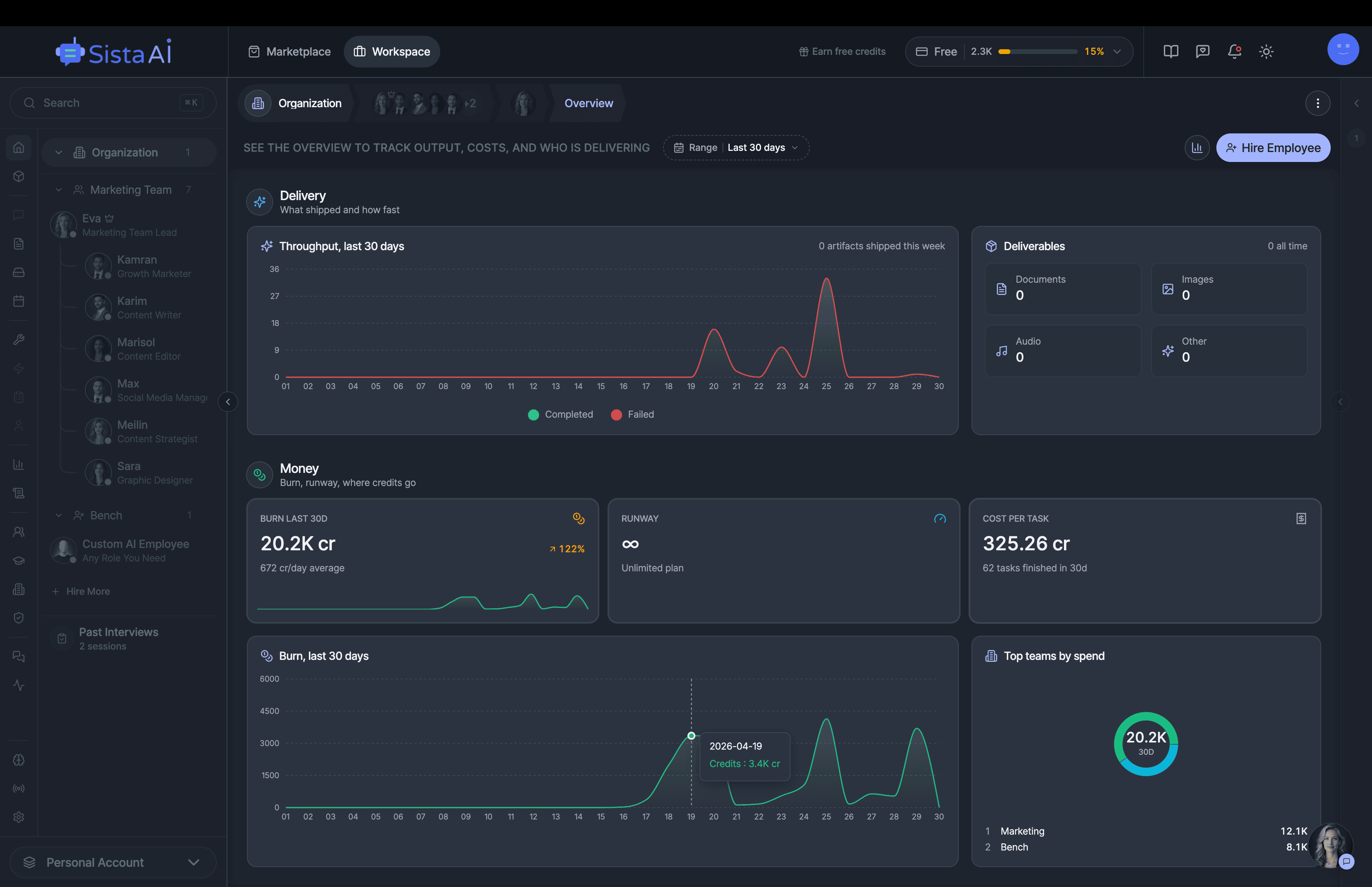
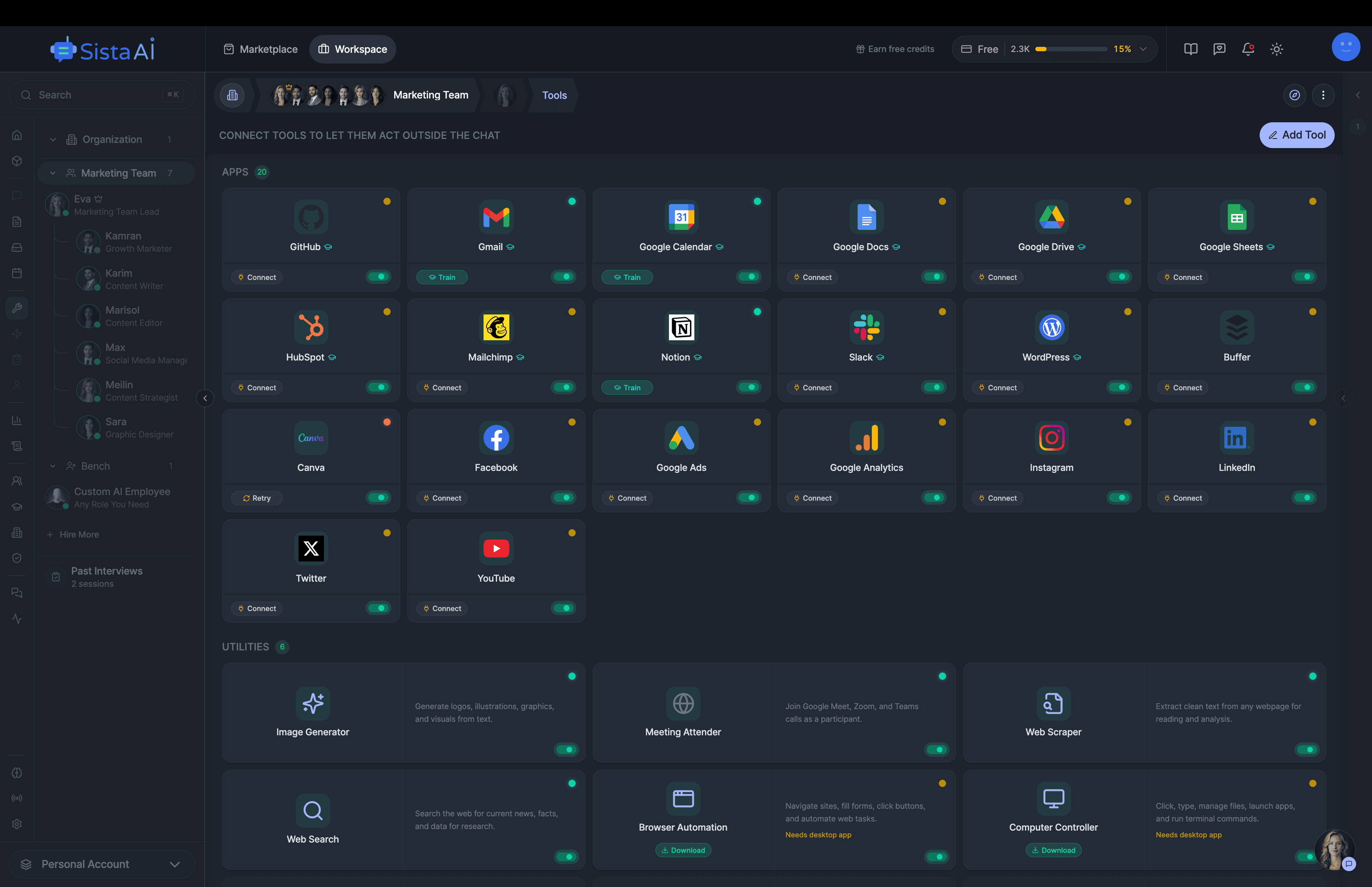
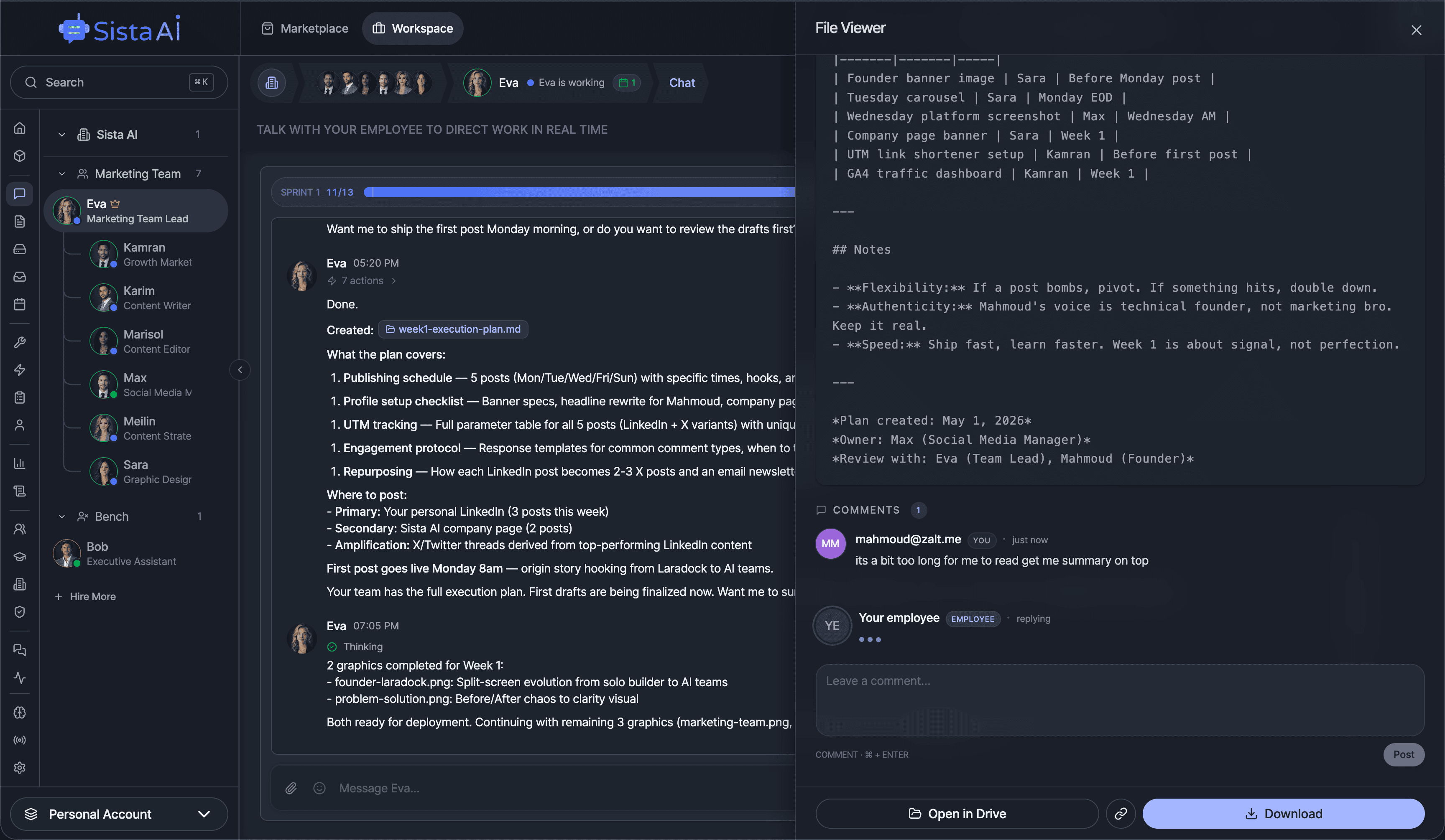
Hire Teams of AI Employees
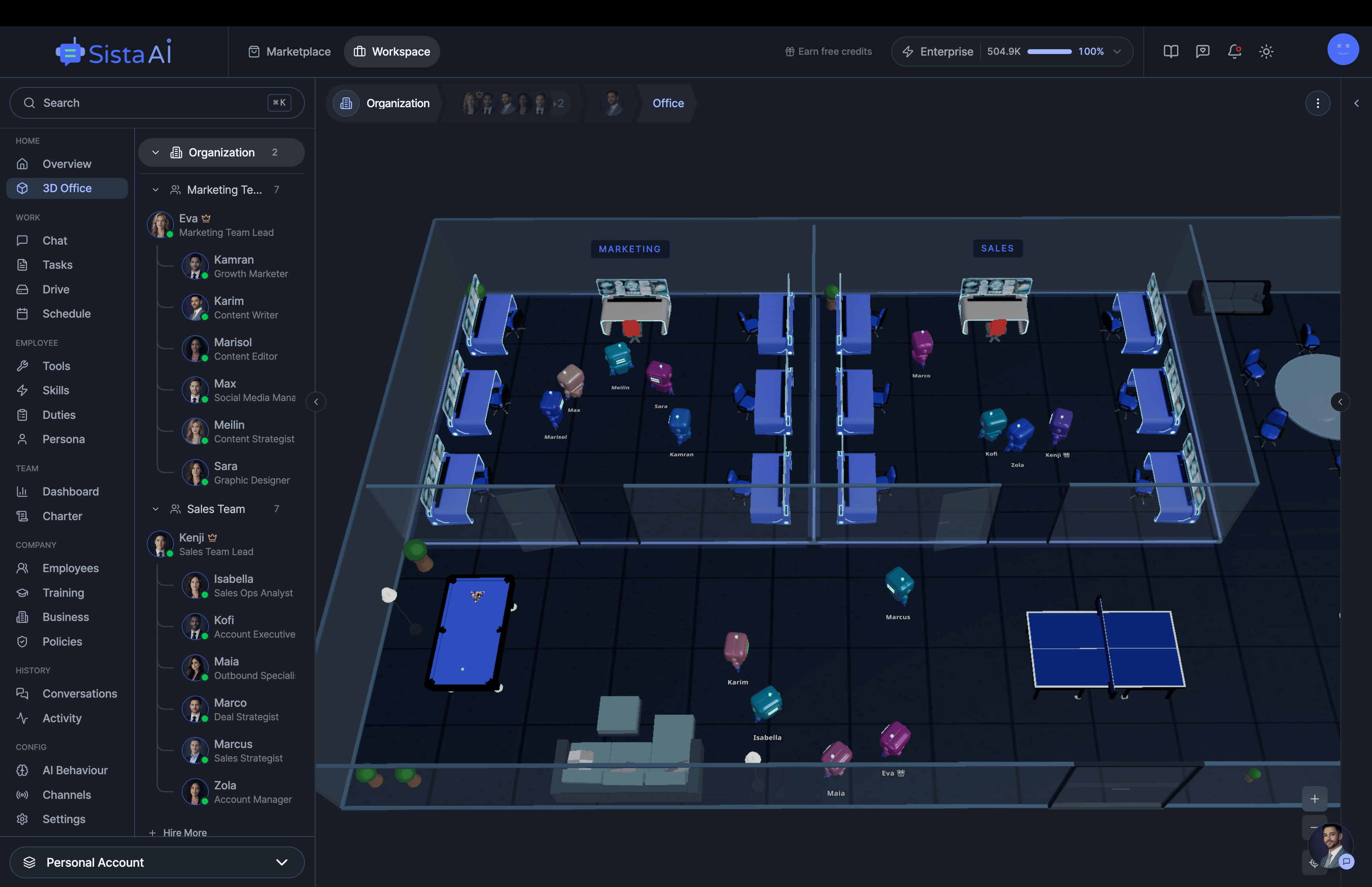
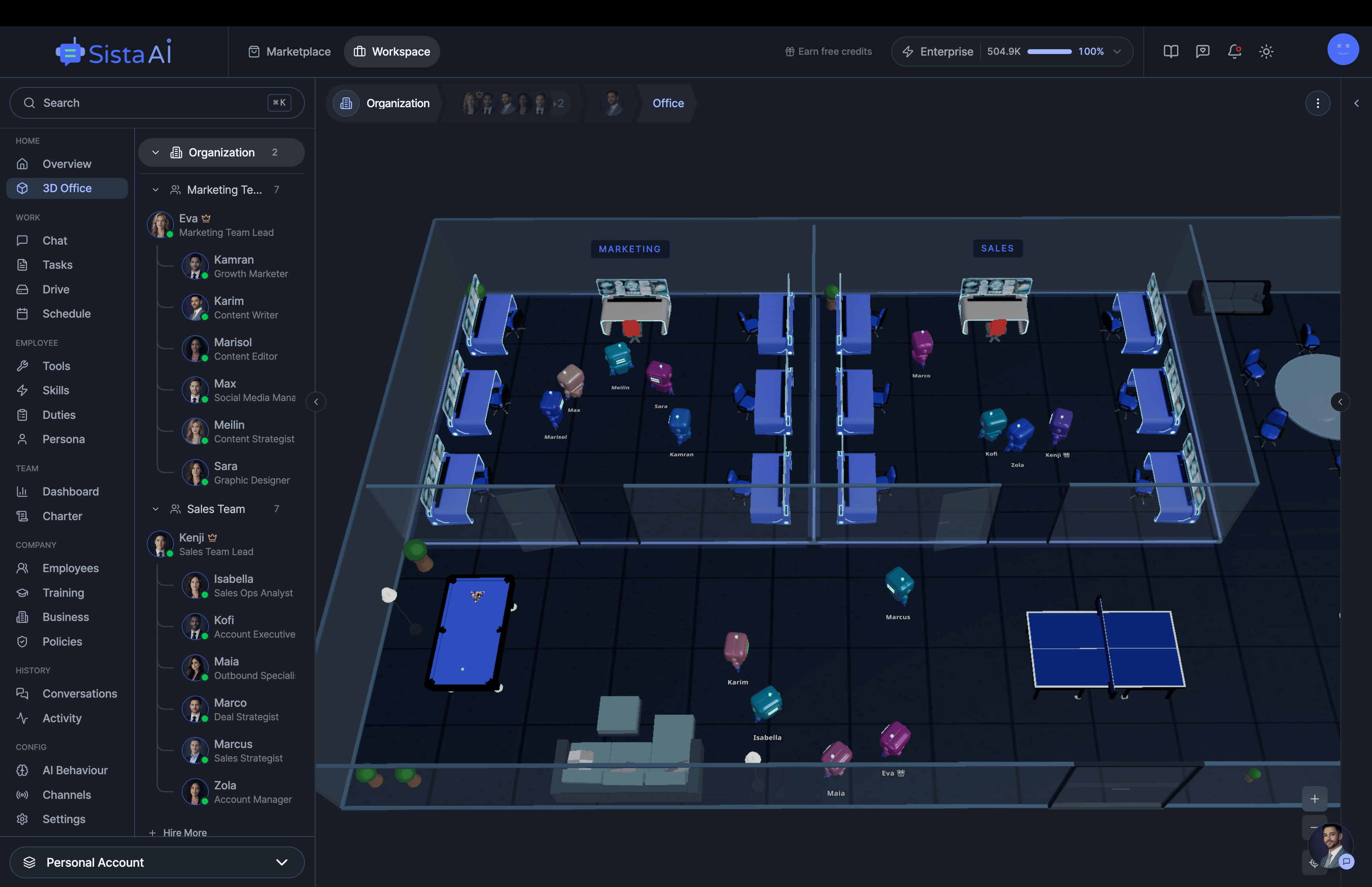
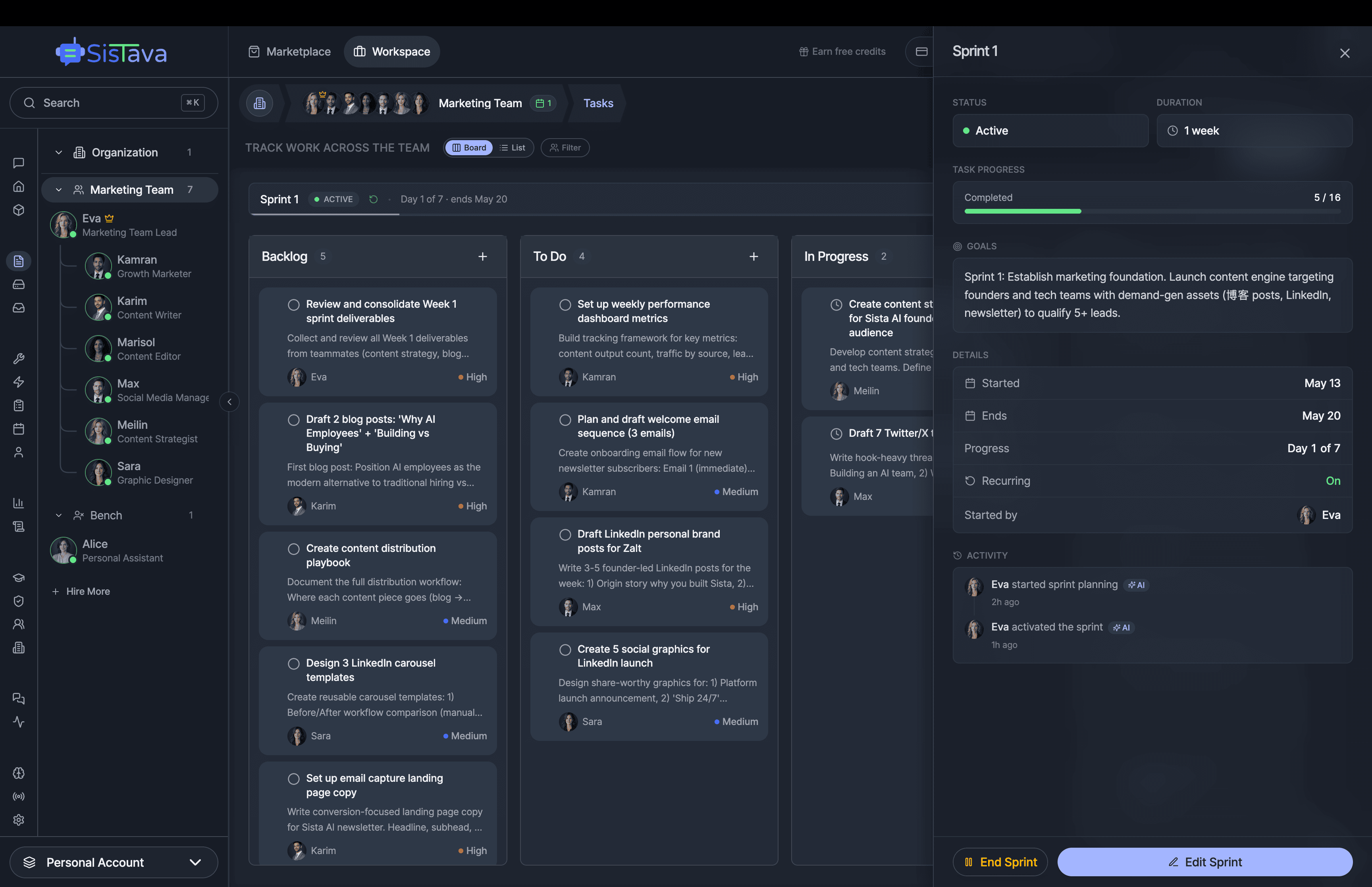
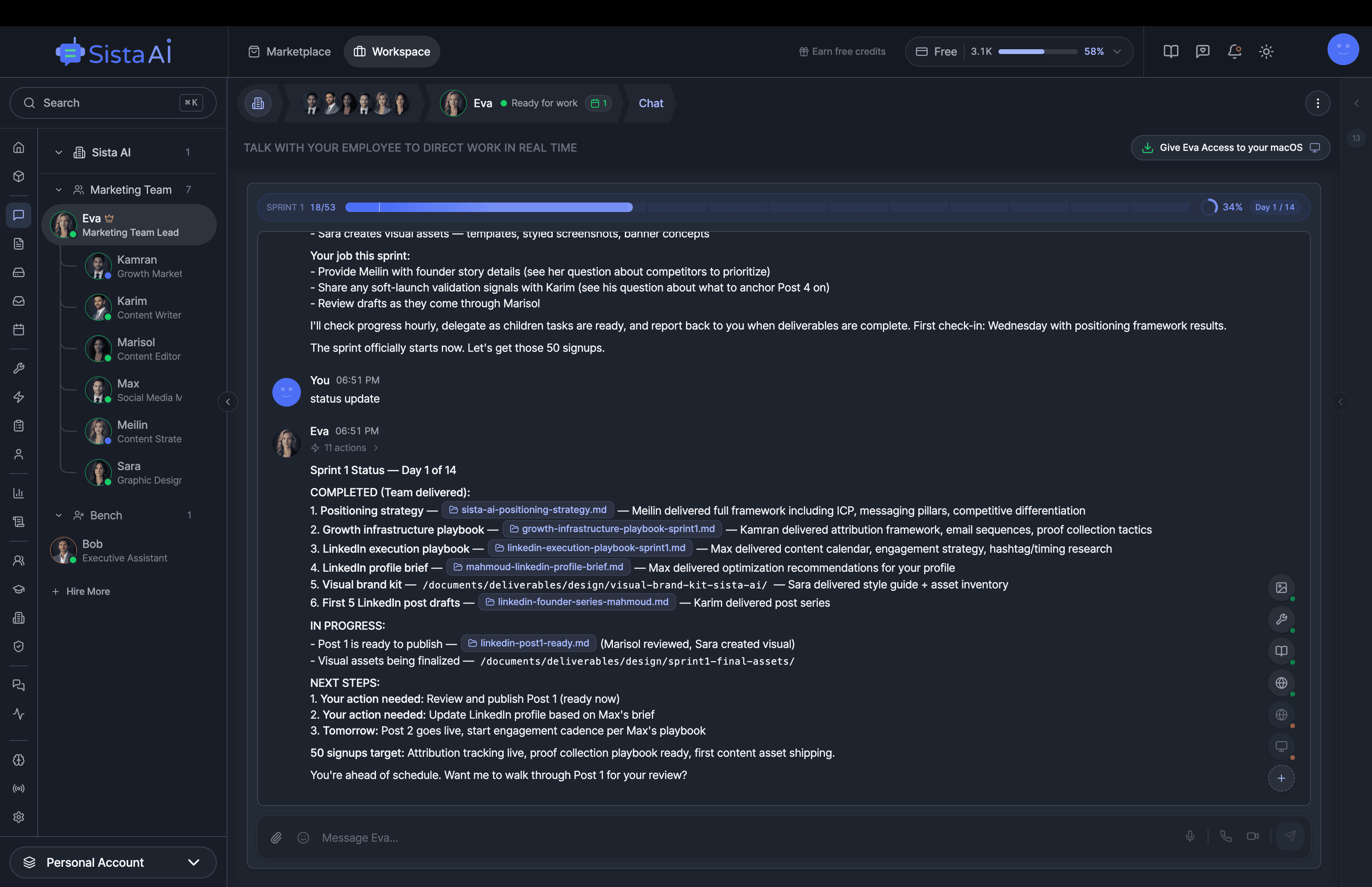
Trained teams of AI employees that work in sprints and follow OKRs to deliver real results. While you focus on strategy.
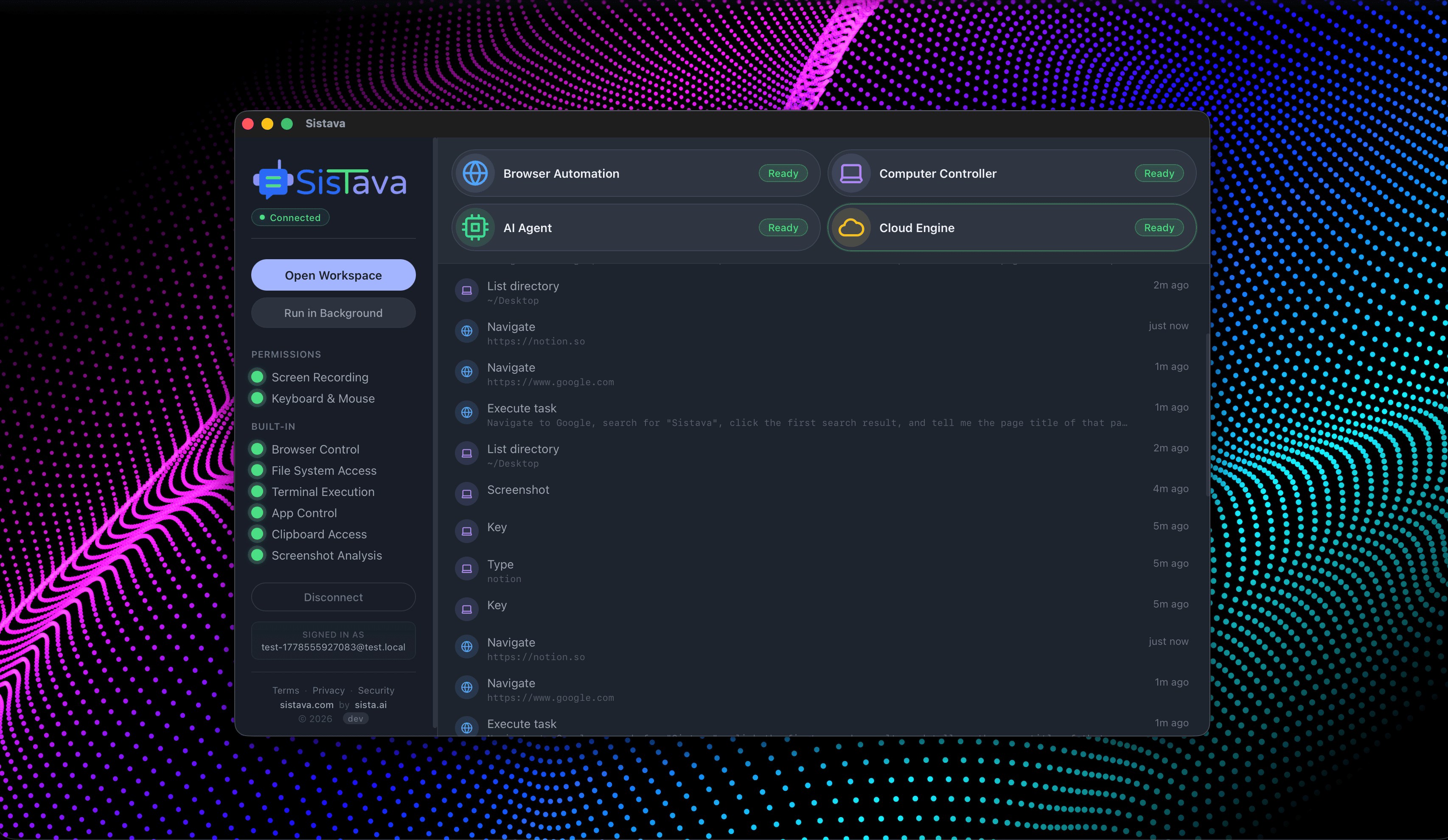
- Control your computer with natural language
- Automate any browser workflow end-to-end
- Attend and summarize your meetings
- Run teams of AI workers that collaborate in sync
- 3D office view to visualize and manage your AI workforce